Accueil > Monitoring > Phishia CTI
Phishia CTI
Anticipate threats, protect your strategic assets
PhishiaCTI division in figures
What is cyber threat intelligence?
Cyber Threat Intelligence (CTI) delivers actionable insights into the threats that matter most to your organization. We continuously monitor and analyze relevant threat activity to help you anticipate risks, prevent incidents, and minimize their impact.

Flare X Phishia, a winning combination
Flare, our web/deep/dark sensor, detects and finds leaks through targeted searches (name/company, BIN, email, phone number, domain/URL, IP, username, password, etc.) and helps manage your external attack surface (EASM). Phishia qualifies, prioritizes, and implements the response (resets, blocks, SIEM/EDR rules).
We therefore classify each leak encountered according to an indicator developed in-house, ranking them by priority of action:
Criticality 1
Minor
Criticality 2
Significant
Criticality 3
Major
Criticality 4
Critical
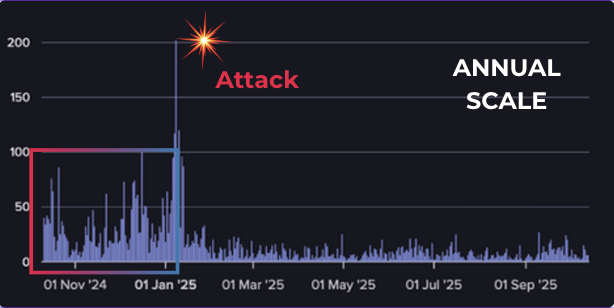
CTI: anticipating attacks
Before each attack, signals appear
Our recommendations
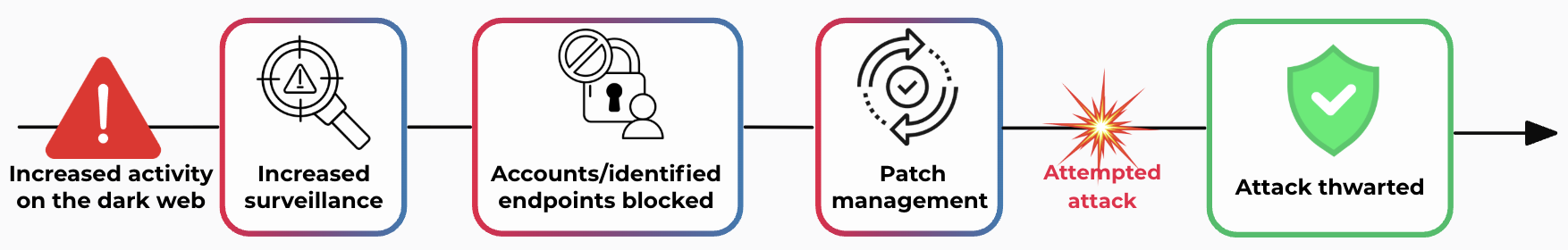
Incident tracking process
We continuously monitor the DW to identify any suspicious activity: sales of access, data leaks, malware, VPNs, attack preparations, exchanges between actors, etc.

Targeted investigation of the service or asset mentioned to assess the actual exposure and concrete risk, in order to distinguish between proven threats and false positives/noise.

Within the authorized framework, we verify the reality and scope of the threat through appropriate checks (e.g., testing the validity of a password).

Depending on the criticality established by our experts, we immediately alert you with a clear playbook, accompanied by a concise report summarizing the information related to the incident.

Phishia CTI Offer
Included in the offer
- Analysis of all data leaks and remediation plan
- Credential validity testing
- Credential criticality prioritization
- Real-time alerts for the most critical issues
- Monitoring of compromised endpoints
- Detailed bi-monthly reporting
Starting at
$30/month
per ID*
* unique identifier that we monitor for you (domain name, IP address, personal email address, etc.)
Phishia CTI Flash
In just 15 days, our Flash CTI service provides you with a clear overview of your exposure on the dark web.
For each leak identified, you will receive a detailed remediation plan and concrete recommendations to permanently reduce your exposure and prevent it from happening again.
1.
Setting the context
Definition of domain names, VIPs, and critical portals to monitor.
2.
ID–Password pair testing
Verification of leaks found on the list of critical portals transmitted.
3.
Advanced VIP search
Targeted analysis of VIP account exposure on open sources and the dark web.
4.
Remediation & security plan
Proposals for actions to remedy and strengthen portal security.
5.
Final report
Comprehensive summary with assessment, prioritization, and next steps.
Phishia CTI Flash Offer
Inclus dans l'offre
- Testing of all credentials reported by Flare
- Plan to strengthen platform security
- Search for leaks concerning X VIPs
- Support in remedying identified leaks
- Delivery of a detailed report
What we need
Domain names
VIP list
Login portals
Our articles
Discover the latest news and trends in SOC & CTI.



