The web iceberg: surface, depth, and dark areas
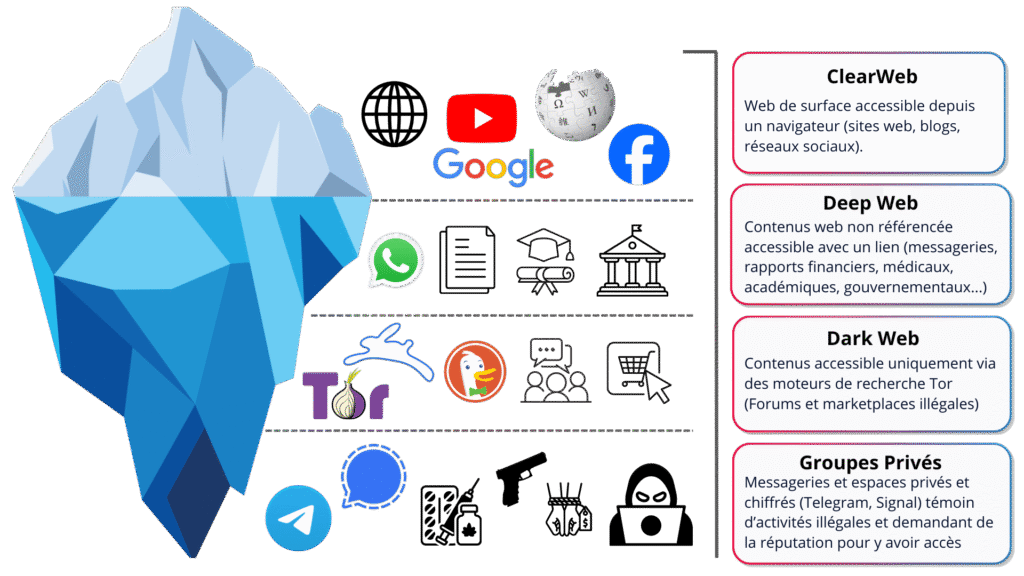
Clear Web – the visible part
The layer “above the surface”: public websites, media, blogs, social networks, found in a few clicks via Google or other search engines.
Deep Web – hidden but legitimate
Below the surface: private spaces (messaging systems, extranets, internal portals), documents and reports accessible only with a link or an account. Not indexed, but perfectly legal.
Dark Web – the risk zone
Access via specific tools such as Tor, with closed forums, marketplaces, and private groups often used for the resale of data, attack tools, or compromised access.
It is precisely in these deep layers that Cyber Threat Intelligence (CTI) will look for weak signals and leaks.
What sensitive information is sold or exposed on the dark web?
On the dark web, attackers do not sell “files” in an abstract way. What they mainly sell are accesses and trust elements that can be used to build an attack.
Here are a few concrete examples taken from cases we regularly encounter at Phishia:
Login credentials
These are username / password combinations for:
- internal portals (intranets, staff portals, donor portals, etc.),
- business services (CRM, HR tools, payment or donation platforms),
- email accounts or administrative accounts.
These credentials may come from:
- a compromised workstation (malware, phishing),
- password reuse from credentials previously leaked elsewhere,
- a negligent service provider.
In our investigations, we regularly see lists containing hundreds of credentials linked to the same domain name, with very different levels of criticality depending on the account involved — ranging from “low-sensitivity” access to accounts capable of modifying financial data or accessing confidential information.
Personal and financial data
For associations and public-sector organizations alike, this may include:
- donor data (contact details, donation history, sometimes SEPA mandates),
- user or beneficiary data,
- information that enables identity theft of an individual or an organization.
Possible consequences include fraud, diversion of donations, loss of trust, and regulatory penalties.
Technical access and infrastructure elements
On dark web forums and marketplaces, it is also common to find:
- access to internal VPNs,
- RDP sessions (remote access to servers or workstations),
- information about unpatched vulnerabilities,
- malware sold specifically to target a given type of organization or technology.
These elements are often used to prepare a broader attack, such as a ransomware campaign.
“Raw” data leaks that require analysis
Leak datasets are not always clean or reliable. They often contain:
- valid and still-active credentials,
- obsolete credentials,
- duplicates,
- false positives.
One of the key roles of a CTI team is precisely to sort, validate, and qualify this data, in order to distinguish real threats from background noise.
Why is this problematic for an organization?
This information allows them to:
- enter your systems without triggering any alarms,
- prepare a targeted scam (phishing, CEO fraud, donation scams),
- resell your data to other criminal groups,
- damage your image if the leak becomes public.
The worst-case scenario: your login details and data have been circulating for months, even years, on specialized forums, and you have no idea.
How Phishia's CTI offering can help you
Cyber Threat Intelligence (CTI) consists of proactively monitoring everything that is happening around your organization across the surface web, deep web, dark web, and within certain private cybercriminal groups.
At Phishia, we rely both on Flare—our web, deep web, and dark web monitoring engine that automatically detects leaks linked to your identifiers (domain names, email addresses, IPs, usernames, passwords, etc.)—and on our analytical expertise to qualify, prioritize, and handle each exposure.
In practical terms, our CTI approach combines several building blocks: continuous monitoring of relevant sources (access sales, data leaks, compromised accounts, malware), targeted checks to verify the validity of certain credentials within a legal framework, OSINT contextualization to understand which services are affected and what the potential impact may be, followed by a criticality assessment with immediate alerting in the event of a serious leak, and a remediation plan (password resets, access revocation, configuration hardening, new SIEM/EDR rules, etc.).
All of this is consolidated into regular reporting, including detailed reports, activity indicators, and tracking of threat trends specifically targeting your organization.
The objective is simple: alert you as early as possible when your information appears on the dark web or high-risk environments, and help you take corrective action before it escalates into a major incident.
Want to find out more? Take a look at our CTI offering:


