There is a frightening adage in cybersecurity: “Attackers only need to be right once. You have to be right 100% of the time.”
But it gets worse. Often, attackers know your network better than you do. Before they even launch a single line of malicious code, they have already mapped out your forgotten servers, exposed technical documents, and test subdomains. How? Thanks to OSINT (Open Source Intelligence) and a discipline that you urgently need to master: ASM (Attack Surface Management).
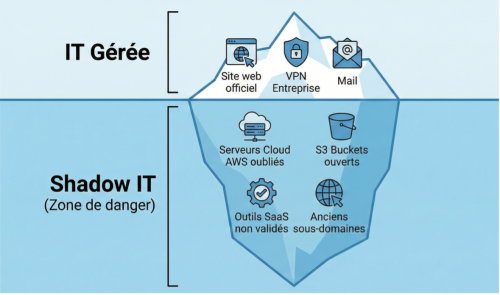
The Hidden Part of the Iceberg: Shadow IT
If you ask your CIO to draw your network, they will show you a clean diagram: headquarters, VPN, secure production servers. This is the theoretical surface.
The actual surface, the one that attackers see, is often much larger and more chaotic. This is what we call Shadow IT:
- A “pre-production” server hastily set up by a developer six months ago and never shut down.
- A public Trello or Notion board containing Wi-Fi credentials.
- A subdomain test.your-company.com that points to an unsecured administration interface.
- GitHub code repositories containing unencrypted API keys.
For an attacker, these are open doors that will not trigger any alarms on your main firewall.
80% of the attack takes place before the intrusion
Ransomware groups do not strike at random. They spend weeks in the Reconnaissance phase. They use OSINT techniques to scan everything that belongs to your company on the public web.
They don’t try to break down your reinforced door (your main firewall). They look for the basement window that’s been left open (that forgotten server running an outdated version).
If you don’t monitor your external attack surface, you’re giving them a considerable head start.
Adopt the attacker's view (“Attacker's View”)
This is where ASM (Attack Surface Management) comes in. Unlike a pentest (penetration test), which is a snapshot at a given moment in time, ASM is continuous video surveillance.
The goal is to continuously map your digital footprint to detect anomalies before they are exploited:
- Discovery: Scan the entire internet to find your assets (IPs, domains, certificates).
- Analysis: Identify vulnerabilities (open RDP port, information leakage).
- Prioritization: Fix critical issues immediately.
Phishia gives you back visibility
At Phishia, we believe that the best defense is a thorough knowledge of your territory. Our services go beyond awareness: we act as a control tower.
Through our Audit and Risk Analysis offerings, coupled with our CTI technology, we map this out for you. We scan the web with the same tools as attackers to tell you exactly what stands out. Don’t let a forgotten server become the entry point for your next crisis. Find out how Phishia reduces your attack surface:


