- stolen credentials,
- VPN access for sale,
- private discussions between cybercriminals,
- access tests on various portals.
Before the attack: when the dark web gets busy
- internal email addresses associated with passwords,
- accounts linked to business portals,
- technical access (VPN, RDP, etc.) resold at low prices.
- more mentions in leak databases,
- more identifiers tested or offered for sale,
- targeted discussions about its services (such as agent portals, administrative accounts, etc.).
- some accesses are tested (connection to portals, verification of credentials),
- “access brokers” resell reliable entry points,
- ransomware groups begin to position themselves.
What well-structured CTI monitoring would have seen
With a mature CTI capability in place, this type of scenario no longer comes as a complete surprise.
In practical terms, CTI enables you to:
Continuously monitor relevant sources: the “traditional” web, the deep web (private spaces, encrypted channels), the dark web (closed forums, marketplaces, private groups), as well as public or semi-private data leak repositories.
The objective is to detect anything related to your organization
(domain names, email addresses, brands, known IP ranges, key portals, etc.).
Qualify what is detected: this is not about saying “we found something,” but about distinguishing what is truly critical. An expired generic account has limited impact, whereas a valid VPN account with elevated privileges or an administrator account on a critical internal portal reaches the highest level of criticality.
For each event, a criticality level is assigned based on the sensitivity of the access, its functional scope, and its potential for exploitation by an attacker.
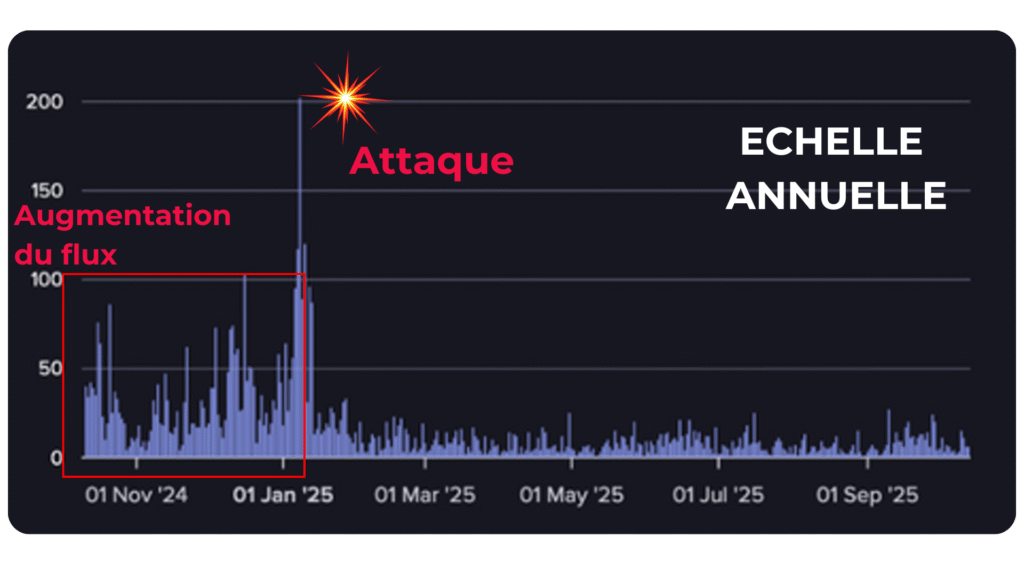
Highlight trends: this is where CTI really shows its value. Rather than treating each leak as an isolated incident, CTI tracks how the volume of leaks linked to your organization evolves over time, identifies unusual spikes in activity, and detects recurring discussions around your accesses or systems.
This is where the classic “before / after” pattern becomes visible: a relatively stable background noise level, followed by a period of abnormal activity ahead of an attack — signaling risk escalation and enabling anticipation instead of reaction.
What Phishia actually does in a CTI approach
Phishia’s CTI offering goes beyond simply “monitoring the dark web.” We apply a structured approach to anticipate attacks and help respond in a timely manner, before the incident escalates into a major crisis.
In the case of an attack that paralyzes a large community or hospital, a truly operational CTI would have made it possible to:
- Be alerted early: as soon as the first truly sensitive leaks occur (critical accounts, valid VPN access, admin credentials, etc.), when activity around the organization deviates from normal.
- Targeted measures to be taken: password resets, token invalidation, authentication reinforcement (MFA, geographic restrictions, IP filtering), verification of exposed portals, rapid audit of access mentioned in the leaks.
- Shift from “reactive” to “preventive”: cut off or closely monitor compromised access, control the most sensitive accounts, prepare the IT department, the CISO, and management for increased risk rather than discovering the leak after the servers have been encrypted.
We cannot promise that every attack would have been prevented 100%, but a well-used CTI greatly reduces the probability of success, limits the extent of the damage… and avoids the general surprise effect.


