In a local authority, everyone works with the same domain name: @city-X.fr, @county-Y.fr, @metropolis-Z.fr, etc.
Civil servants, departments, schools, municipal police, social services, culture, sports, elected officials, sometimes external service providers, etc.
The result: hundreds, sometimes thousands of accounts that rely on the same servers, the same portals, the same systems.
For an attacker, this is a golden opportunity:
- a single domain to target,
- tons of credentials to retrieve,
- and very often many leaks already present on the dark web.
Cyber Threat Intelligence (CTI) is precisely there to shed light on this and do a real “clean-up” in terms of exposure.
Why do communities leak so much on the dark web?
Local authorities, despite themselves, are ideal targets for cybercriminals.
They have a large number of employees (and therefore a huge number of accounts), passwords that are often reused between internal tools and external services, accounts that remain active even after people have changed jobs or left the authority, not to mention the many professional portals exposed on the internet (citizens, employees, schools, social services, etc.).
Over time, all of this leaves traces on the dark web. We see the appearance of:
- lists of local government email addresses with their associated passwords,
- logins for internal or partner portals,
- and sometimes even sensitive technical access (VPN, RDP, administration consoles, etc.).
The most worrying thing is that this situation remains completely invisible to the local authority: the system continues to run, employees work as normal… even though compromised access details are circulating and can be exploited at any time.
Why these leaks are so dangerous for a community
These leaked credentials allow:
- access to citizen portals (online procedures, school registrations, extracurricular services, etc.),
- access internal administration interfaces,
- reach more sensitive services (municipal police, social services, urban planning, etc.),
- and jump from one service to another, or even from the web to the internal IT system.
Not all leaks are created equal, but some are clearly explosive. This is the case, for example, with accounts that give access to social, educational, or administrative data, accounts linked to sensitive services (municipal police, finance, urban planning, etc.), or even technical access that allows users to bounce to other internal servers.
The same email/password combination can be used to log in to a citizen portal, a business extranet, and then, through a series of accesses, to obtain higher privileges in the information system. For an attacker, this is an ideal entry point for preparing a ransomware attack, carrying out targeted fraud, siphoning off sensitive data, or simply reselling this access to other criminal groups.
At Phishia, we have developed a criticality indicator that allows us to classify and prioritize each leak in order to focus our efforts where the risk is actually highest.
What the CTI brings to local authorities
When applied to local authorities, CTI involves monitoring, analyzing, and processing everything that circulates about them outside their own systems.
- Finally having a clear view of exposure
Instead of worrying about vague issues such as “we must have leaks somewhere…”, CTI allows you to know how many identifiers linked to the local authority’s domain are circulating, what types of accounts are affected, which services or portals are mentioned, and which accesses still appear to be active. - Distinguish between noise and real risk
A good CTI does more than just list leaks: it qualifies what is outdated or already invalid (low risk), what is still exploitable (high priority), and what could potentially open up access to sensitive data or allow internal rebound (critical priority). - Turn information into security actions
Based on this information, the local authority can reset or deactivate exposed accounts, strengthen the security of the portals concerned (strong authentication, filtering, restrictions), adjust its detection rules (SIEM, EDR, firewalls, etc.) and raise awareness among the most exposed agents.
With this approach, we move from “we suffer” to “we control.”
The CTI flash audit: cleaning up the dark web
For local authorities that have never really looked at what is circulating about them, a CTI flash audit is an excellent starting point.
The idea is simple: in a few weeks, obtain a clear picture of the situation, deal with the emergency, and lay the foundations for the future.
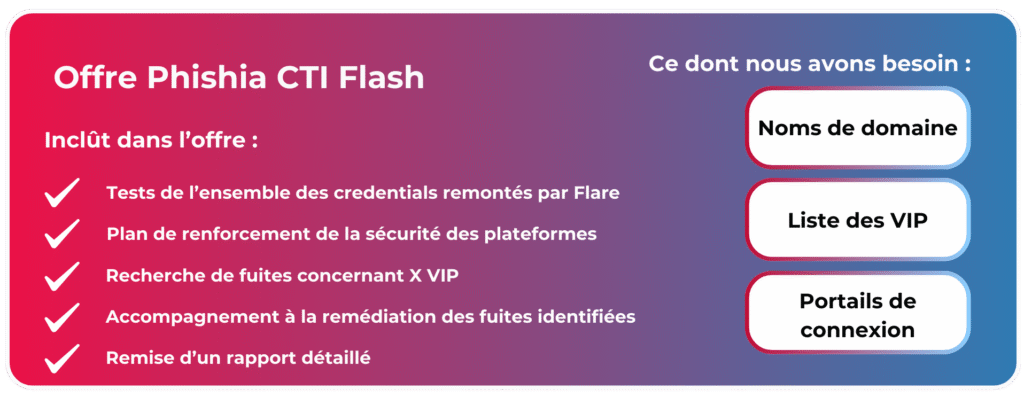
A CTI flash audit first defines the scope of monitoring: the local authority’s domain names, critical portals and services, and sensitive profiles (elected officials, management, key functions).
It then searches for existing leaks: circulating credentials (email + password), mentions of the local authority’s services or applications, and access or data offered for sale.
Thirdly, the audit tests and qualifies the leaks: verification of what is still valid in a controlled environment, measurement of the potential impact (accessible data, possibilities for rebound), classification of cases by level of criticality.
On this basis, it proposes a concrete remediation plan: accounts to be reset or blocked, hardening of exposed portals, measures to limit the reappearance of new leaks (awareness, password policies, MFA, etc.).
Finally, the audit concludes with a usable report, including a summary overview for decision-makers, specific technical details for the IT department/CISO, and a clear prioritization of actions.
In short, after a flash audit, the organization knows what is circulating, what is dangerous, and what has been neutralized or needs to be neutralized.
Phishia's role in this process