Forget the image of the hacker in a hoodie typing lines of fluorescent green code all night long to brute-force your servers. In 2025, the reality is much more mundane, and frightening: your network access may have already been sold this morning, for the price of a Big Mac meal.
Welcome to the era of Stealer Logs, the silent threat that renders your password policies obsolete.
The mechanism: How your digital identity is “zipped”
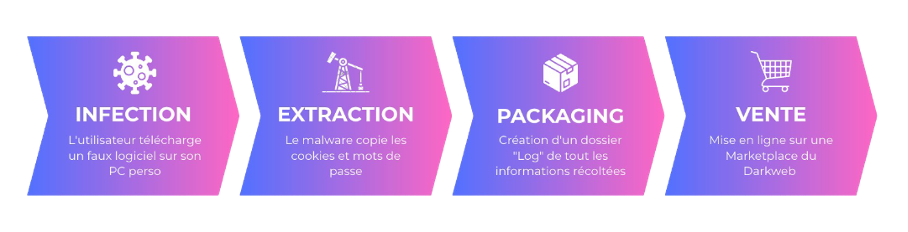
Infostealers (such as Lumma, RedLine, and Vidar) are discreet malware programs. They don’t need to break into your systems. They often install themselves via cracked software downloaded by a remote worker, or an innocuous attachment in a personal email.
Once active on the machine, the malware doesn’t just steal passwords. It sucks up everything:
- The logins saved in the browser.
- Credit card information.
- Browsing history.
- And above all: session cookies.
This is where the critical danger lies.
Why MFA won't always save you
This is a rude awakening for many CIOs. Multi-Factor Authentication (MFA) is often thought to be the ultimate defense. But if an attacker steals your valid session cookie via a log stealer, they don’t need your password or SMS code. They import this cookie into their own browser and the target site (your CRM, your Office 365 access, your VPN) thinks it’s you. They are already logged in.
The crime supermarket
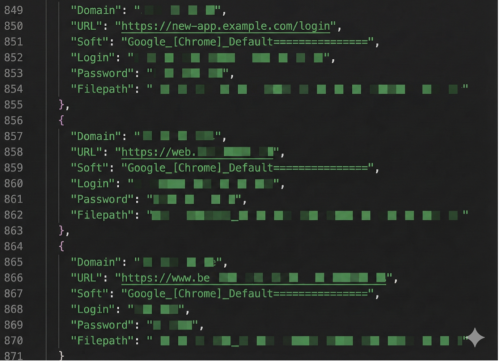
This stolen data does not remain on the hacker’s computer. It is aggregated on a massive scale on automated marketplaces (such as Russian Market or private Telegram channels).
The business model is industrial. A “log” (the complete file of a victim or group of computers) generally sells for around $10. For this price, the buyer gains access to all accounts: Netflix, Facebook, and even their company’s VPN access.
This is how most ransomware attacks start these days: with a simple $10 purchase made weeks before the final attack.
Take back control with CTI
Digital hygiene is essential, but it relies on humans, who are fallible. You can’t prevent an employee from accidentally installing malware on their personal PC, but you can find out if their work credentials have been leaked.
Cyber Threat Intelligence (CTI) is not just about looking at your internal logs, but also monitoring the outside world.
At Phishia, we continuously scan these underground markets. We can detect if credentials belonging to your @your-company.com domain are currently for sale in logs, even if the infection occurred on an employee’s personal computer.
Immediate action: The CTI Flash audit
Don’t be left in the dark. Knowledge is power.
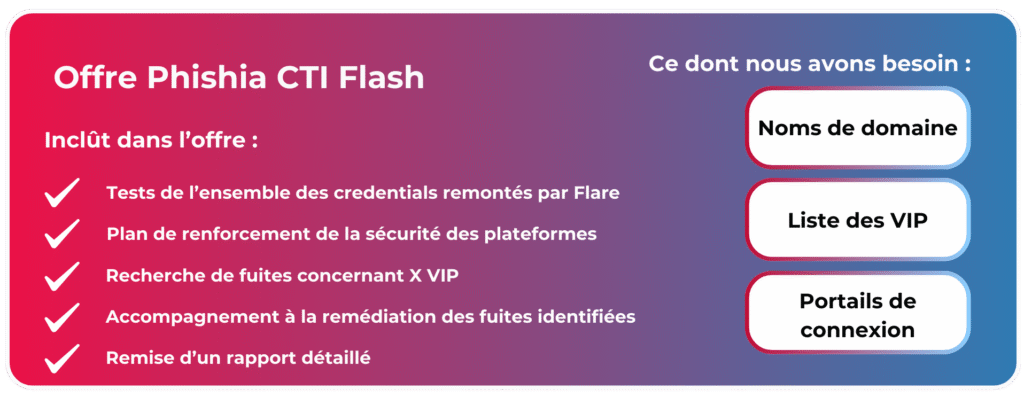
To launch our CTI offering, Phishia is offering a pragmatic approach: The CTI Flash Offer. This is a one-off audit to provide an immediate assessment of your exposure.